Installation.
CAUSES OF WIN32 CONFICKER
When executed, the worm copies itself in some of the the following locations:
- %system%\%variable%.dll
- %program files%\Internet Explorer\%variable%.dll
- %program files%\Movie Maker\%variable%.dll
- %appdata%\%variable%.dll
- %temp%\%variable%.dll
A string with variable content is used instead of %variable% .
The worm loads and injects the %variable%.dll library into the following processes:
The worm loads and injects the %variable%.dll library into the following processes:
- explorer.exe
- services.exe
- svchost.exe
The worm registers itself as a system service with the name combined from the following strings:
- Boot
- Center
- Config
- Driver
- Helper
In order to be executed on every system start, the worm sets the following Registry entry:
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\
Run]
- "%variable_name%" = "rundll32.exe "%system%\%variable%.dll",
%random_string%"
The following Registry entries are set:
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\
Run]
- "%variable_name%" = "rundll32.exe "%system%\%variable%.dll",
%random_string%"
The following Registry entries are set:
- [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\%random
service name%\Parameters]
"ServiceDll" = "%system%\%variable%.dll"
- [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\%random
service name%]
"Image Path" = "%System Root%\system32\svchost.exe -k netsvcs"
A string with variable content is used instead of %random service name% .
The following Registry entries are deleted:
- [HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\
CurrentVersion\explorer\ShellServiceObjects\
{FD6905CE-952F-41F1-9A6F-135D9C6622CC}]
"wscsvc" = "%filepath%"
- [HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\
CurrentVersion\Run]
"Windows Defender" = "%filepath%"
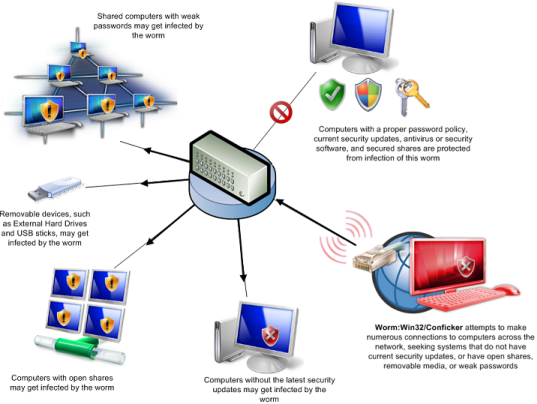
Spreading
The worm starts a HTTP server on a random port.t connects to remote machines to port TCP 139, 445 in attempt to exploit the Server Service vulnerability.
If successful, the remote computer may attempt to connect to the infected computer and download the copy of the worm.This vulnerability is described in Microsoft Security Bulletin MS08-067 .
Spreading via shared folders.The worm tries to copy itself into shared folders of machines on a local network.
The following usernames are used:
- %username%
The following passwords are used:
- 123
- 1234
- 12345
- 123456
- 1234567
If successful the following filename is used:
\\%hostname%\ADMIN$\System32\%variable%.dll
The worm schedules a task that causes the following file to be executed daily:
rundll32.exe %variable%.dll, %random_string%
Spreading on removable media
The worm copies itself into existing folders of removable drives.
If successful the following filename is used:
The worm schedules a task that causes the following file to be executed daily:
rundll32.exe %variable%.dll, %random_string%
Spreading on removable media
The worm copies itself into existing folders of removable drives.
If successful the following filename is used:
- %drive%\RECYCLER\S-%variable1%\%variable2%.%variable3%
A string with variable content is used instead of %variable1-3% .
The worm creates the following file:
- %drive%\autorun.inf
Thus, the worm ensures it is started each time infected media is inserted into the computer.
Other information
The following services are disabled:
- Windows Security Center Service (wscsvc)
- Windows Automatic Update Service (wuauserv)
- Background Intelligent Transfer Service (BITS)
- Windows Defender Service (WinDefend)
- Windows Error Reporting Service (ERSvc)
- Windows Error Reporting Service (WerSvc)
If the current system date and time matches the condition the worm will attempt to download several files from the Internet.
The worm runs only encrypted and properly signed files.The file is stored into the following folder:
- %temp%
If successful the following filename is used:
- %variable%.tmp
The worm may set the following Registry entries:
The worm runs only encrypted and properly signed files.The file is stored into the following folder:
- %temp%
If successful the following filename is used:
- %variable%.tmp
The worm may set the following Registry entries:
- [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\
SharedAccess\Parameters\FirewallPolicy\StandardProfile\
GloballyOpenPorts\List]
- "%port number%:TCP" = "%port number%:TCP:*:Enabled:%variable%"
The performed data entry creates an exception in the Windows Firewall program.
HOW TO REMOVE WIN32.AA CONFICKER
you have to download win32 conficker removal tool to remove this virus.

No comments:
Post a Comment